The risk
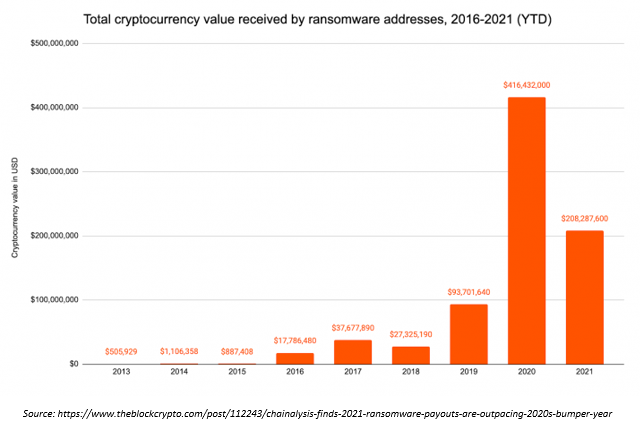
While traditional risks, like data theft, hacked servers, and natural disasters are still prevalent, ransomware is the one that generates the most headlines today. It's exploded over the last few years as malicious actors become smarter and continue to adapt despite business's security measures. We see huge companies being hit with ransomware, but that doesn't mean small businesses aren't targets, too. They just don't make the headlines.
Tip #1: Business continuity and disaster recovery - what's the difference?
Business continuity (BC) is the continuation of business through an adverse event, from natural disasters to server room malfunctions to malicious situations.
Disaster recovery (DR) is your return to normal business operations. It's where you use your BC plan to work your way through the adverse event. Here, your Recovery Time Objective (RTO) and Recovery Point Objective (RPO) must be defined.
-
- RTO: how fast can you get back online? Using backups as an example, can we restore your backups in an hour, two hours, a day, etc.?
- RPO: how far back in time do we have to go (how old are your backups)? Are they a day old, a week old, two weeks old, etc.? For a business with more frequent changes going, the shorter the RPO, the better.
Tip #2: Test your plan
It is extremely important to test your business continuity plan before a situation hits, not during. This will help you identify the gaps in your plan and modify as needed. It also allows you to prioritize what systems need to be brought online first, because it's very unlikely that everything can be resolved right away.
This plan should not only include bringing your data back online, it also should be looked at as a communication component. You'll need to include warranty information, insurance information, vendor contacts, attorney contacts, and so on.
Cybersecurity insurance is also something that every business should have, because a ransomware recovery can be extremely expensive. It's not uncommon for these fees to be more than $100k. Factors include financial loss, reputational damage, operational downtime, legal action against your company, loss of sensitive data, hiring a forensic team to resolve the incident, and of course, paying the actual ransom itself.
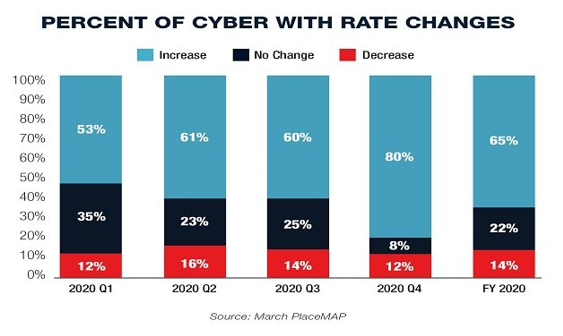
You should also ensure that your insurance coverages are adequate. Every business has different needs, and it's important to make sure your coverages reflect them. Not only that, but if your organization is actively growing, this means your needs are actively changing and should be assessed on an annual basis, if not more often.
Tip #3: Cloud misconceptions
Many people believe that the cloud is secure, and that the cloud is backed up. While the cloud can be secure and backed up, it's not automatically that way. This is why having conversations with your vendors around this subject will bring clarity as to what your cloud posture is. Are they backing up your information, and if so, how often? If they are not, what add-ons should you implement so that they are taking care of this important piece of your business?
Microsoft posted a shared responsibility document where they outline what their responsibility is, and what you need to take care of. This is a great tool to use to build your plan around.
Summary
- Have a solid BC/DR plan
- Make sure your cybersecurity insurance covers what is appropriate based on your needs
- Make sure the data is part of your plan - don't assume that because it's in the cloud that it's secure and recoverable
How can we help?
Interested in discussing this further? If you are one of our partners, please reach out to your Partner Success Manager, or email partnersuccess@entechUS.com. If you are not a partner, please contact us here, or email us at hello@entechUS.com